/ Cybersecurity / Threat Hunting
Autonomous hunts. Machine speed.
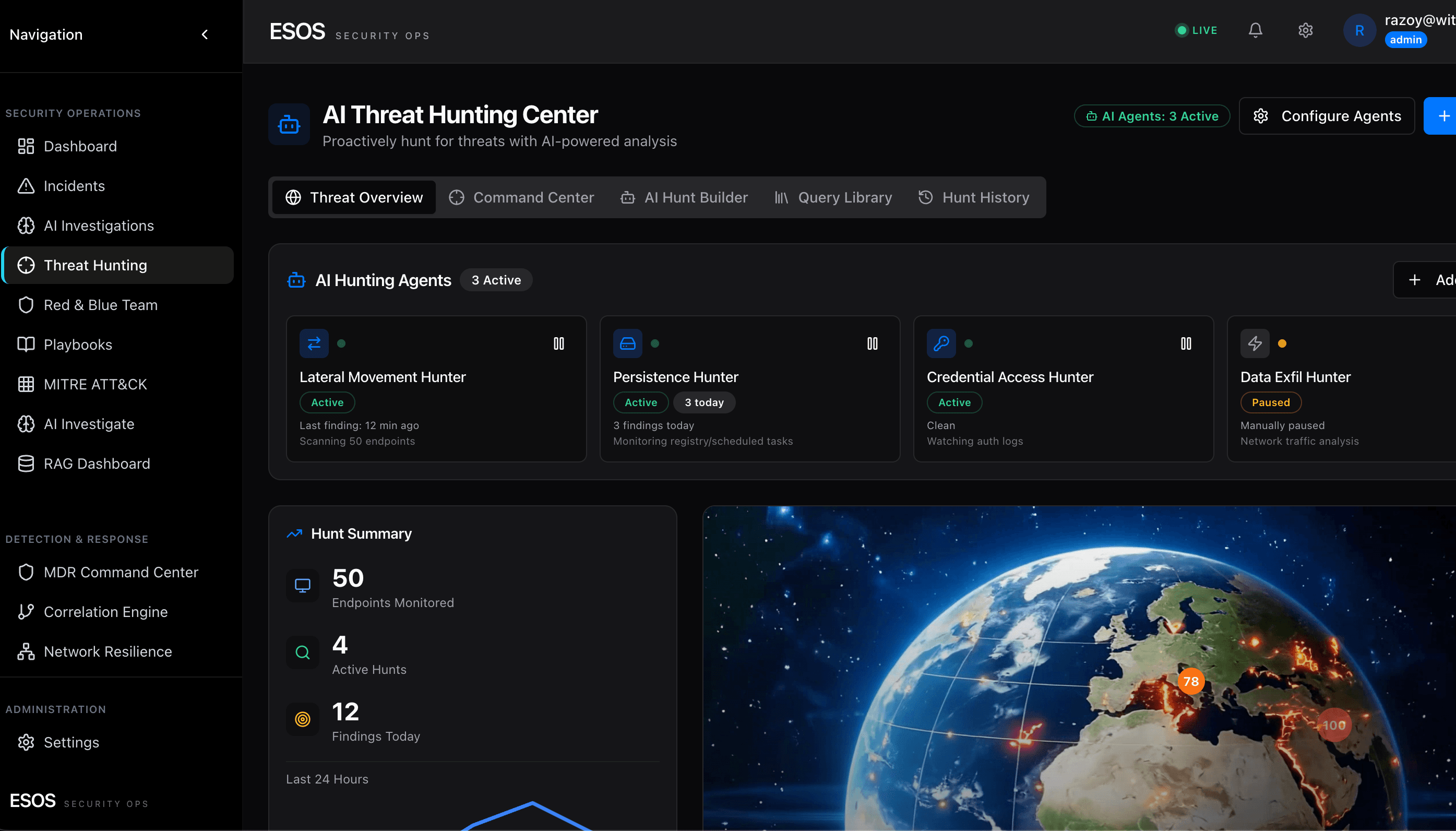
ESOS Threat Hunting turns proactive defense from a specialist art into a continuous, scalable engineering discipline. AI agents run hypothesis-driven hunts 24/7 — anchored to MITRE ATT&CK, federated across every telemetry source you own, and grounded in Astute RAG so every finding ships with cited evidence. Your team reviews conclusions. The AI does the hunting.
- Hundreds of MITRE ATT&CK-mapped hypotheses execute continuously — no analyst trigger required
- Ask in plain English; agents federate the query across SIEM, EDR, identity, cloud, network, and OT
- Findings auto-promote to investigations with cited evidence, kill-chain narrative, and proposed response
- Astute RAG grounds every hunt in 50M+ vectorized CVE / ATT&CK / actor / advisory documents

/ What you get
Everything you need. Nothing you don't.
Hypothesis-driven, continuously generated
A living library of falsifiable hunt hypotheses — derived from ATT&CK techniques, CISA KEVs, the active threat-intel corpus, your specific attack surface, and prior incidents — runs on rotation. New hypotheses generate automatically when ATT&CK adds sub-techniques or a CTI feed reports a fresh TTP.
Natural-language query console
Ask in English: "Show me every privileged user who authenticated from a new geolocation in the last 24 hours and then accessed a code repo." Agents translate intent, federate across data sources, normalize results, and return a written answer with cited evidence and a one-click pivot into deeper investigation.
Investigation agent pipeline
Orchestrator decomposes the question · Enrichment Agent pulls TI, asset criticality, identity posture · Correlation Agent assembles the entity graph · Analysis Agent scores risk, maps to ATT&CK, reconstructs kill chain, writes narrative. Multi-LLM router optimizes cost, latency, and accuracy per query.
Federated across your telemetry
Native connectors for Microsoft Sentinel & Defender, CrowdStrike Falcon, Intune, Active Directory, Entra ID, Kentik, Freshservice, Dragos (OT), and the full ESOS stack. Bidirectional: agents read events for hunting and push enrichments, detections, and case material back into the source of record.
Astute RAG knowledge base
50M+ vectorized documents — CVEs, ATT&CK techniques, threat-actor profiles, advisories, and historical incident outcomes — ground every hunt in current intelligence and prevent hallucination. Every answer carries citations.
MITRE ATT&CK coverage heat map
Real-time visualization of which techniques you detect, which you don't, and which you've hunted in the last 7 / 30 / 90 days. Drill from any technique into the hypotheses, detections, and incidents that cover it. Customers carry an average of 196 of 201 enterprise techniques under active coverage.
Kill-chain reconstruction
When a hunt confirms malicious activity, ESOS orders the observed events into a temporal kill chain, maps each stage to ATT&CK tactics, and produces a single-page incident narrative suitable for SOC review or executive briefing.
Semantic investigation canvas
Every confirmed hunt opens into an entity-relationship graph — users, devices, IPs, files, processes — with the AI narrative on one side and supporting evidence on the other. The "CSI board" view your analysts have always wanted.
Playbook hand-off via WIT OS Flows
Confirmed findings can trigger a one-click playbook through WIT OS Flows — isolate host, disable account, rotate credentials, open Freshservice ticket, notify on-call — or auto-execute when the hunt clears your configured confidence and authorization thresholds.
/ Inside the cockpit
Hunts as continuous engineering.
ATT&CK heat map, hypothesis library, natural-language query console, and the semantic investigation canvas — all in the same operator surface. Findings flow into evidence packs, detection-as-code, and WIT OS Flows playbooks without leaving the screen.

Ready to run on WIT OS?
Talk to the team about a managed deployment, a pilot, or a custom agent — we typically respond within an hour.
/ FAQ
Frequently asked questions
How is AI-driven threat hunting different from a SIEM rule?
A SIEM rule fires when a specific pattern matches; it catches known knowns. AI-driven threat hunting asks falsifiable hypothesis questions against telemetry — "Is any privileged user authenticating from a new geolocation and then accessing a code repo?" — and runs hundreds of them continuously across SIEM, EDR, identity, cloud, network, and OT data. It catches things you didn't know to write a rule for, including living-off-the-land tradecraft that doesn't trip signatures.
Where does the threat hunting actually run?
Inside ESOS — the WIT OS security operations orchestrator. ESOS's investigation agents (Orchestrator, Enrichment, Correlation, Analysis) decompose hunt questions, federate queries across your telemetry sources, normalize results, and write the narrative. Findings flow into the same operator surface as MDR alerts, threat intel, and pentest results.
What grounds the AI so it doesn't hallucinate?
Astute RAG. Every hunt is grounded in a vectorized corpus of 50M+ documents — CVEs, ATT&CK techniques, threat-actor profiles, advisories, and historical incident outcomes — with citations on every answer. The Dynamic LLM Router selects the right model per query (fast triage vs. deep reasoning), optimizing accuracy, latency, and cost.
Do we need to give up our existing SIEM or EDR?
No. ESOS Threat Hunting is federated, not replacement. Native bidirectional connectors for Microsoft Sentinel & Defender, CrowdStrike Falcon, Intune, Active Directory & Entra ID, Kentik, Freshservice, Dragos (OT), and 60+ more. The hunting layer sits on top of whatever telemetry you already have.
How fast does a pilot reach full operating capability?
Typically 30 to 45 days, including connector configuration, hypothesis library tuning to your environment, and SOC team enablement. Customers reach detection-coverage parity with mature SOCs in under 60 days without hiring detection engineers.