/ Cybersecurity / Exposure Management
See every exposure. Fix what matters first.
Modern enterprises don't have a vulnerability problem — they have an exposure problem. Internet-facing services drift, identities sprawl, cloud accounts spin up faster than they're inventoried, and a CVE alone tells you nothing about whether it's reachable. WIT ONE delivers exposure management as a joint engagement with Arctic Wolf — their managed Attack Surface Management discovers what's exposed; WIT ONE's Vulnerability Management (built into ESOS) prioritizes what to fix based on real-world exploitability, business context, and attack-path reachability.
- Arctic Wolf delivers continuous Attack Surface Management — external + cloud + identity asset discovery
- ESOS Vulnerability Management adds reachability + exploit context: CVSS · EPSS · KEV · attack-path
- Unified risk score per asset · prioritized remediation list · SLA-tracked workflows
- Compliance evidence assembles itself — SOC 2 CC4, ISO 27001 A.5.7 / A.8.8, PCI-DSS Req 11

/ What you get
Everything you need. Nothing you don't.
Attack Surface Management · Arctic Wolf
Arctic Wolf's managed ASM continuously discovers every internet-facing asset, every cloud account, every shadow service. Subdomain enumeration, certificate-transparency monitoring, exposed-port discovery, and identity-perimeter scanning — all run as part of their Concierge Security Team engagement.
Vulnerability Management · in ESOS
Built into our ESOS orchestrator. Ingests scan output from Tenable, Qualys, Rapid7, Wiz, and Snyk; deduplicates findings; enriches with exploit availability; and routes remediation tickets to ServiceNow, Jira, or Freshservice. Complements Arctic Wolf's ASM with the prioritization and execution layer.
Exploit-aware prioritization
Every vulnerability scored on four signals: CVSS severity, EPSS exploit probability, CISA KEV catalog membership, and asset criticality from your CMDB. A medium-CVSS vuln on a public-facing crown-jewel server with KEV inclusion outranks a critical-CVSS vuln on an isolated lab box.
Attack-path reachability
Not every exposed vulnerability is reachable. ESOS overlays your network topology, identity tier model, and segmentation policies so the prioritization layer can mark vulns that an attacker can actually exploit from the internet — vs. ones requiring four pre-conditions that don't exist in your environment.
SLA-tracked remediation workflows
Findings flow into your existing ticketing system with AI-generated context: severity, business impact, recommended fix, owner, dependency chain. SLA timers run per finding; escalations fire automatically; closures route back to the source of record. WIT OS Flows wires the whole loop.
Continuous compliance evidence
Every scan, every finding, every remediation, every retest is audit-grade evidence. SOC 2 CC4 (Monitoring), ISO 27001 A.5.7 (Threat Intelligence) and A.8.8 (Vulnerability Management), PCI-DSS Requirement 11, and HIPAA Risk Analysis are continuously satisfied — auditors get artifacts on demand instead of quarterly fire drills.
Identity exposure surfaced
Exposure management isn't only about IP addresses. Stale service accounts with admin rights, OAuth grants to suspicious apps, privileged accounts without MFA, dormant accounts with active credentials — all surfaced as exposure findings alongside CVEs, mapped to the same prioritization model.
From discovery to closure in one loop
Arctic Wolf discovers, WIT ONE prioritizes and remediates, both teams share the same operator surface, and the same evidence trail satisfies every compliance framework. No vendor seam, no duplicate dashboards, no "who owns this finding?" — one engagement, one accountability chain.
/ Inside the joint engagement
Two specialist consoles. One exposure surface.
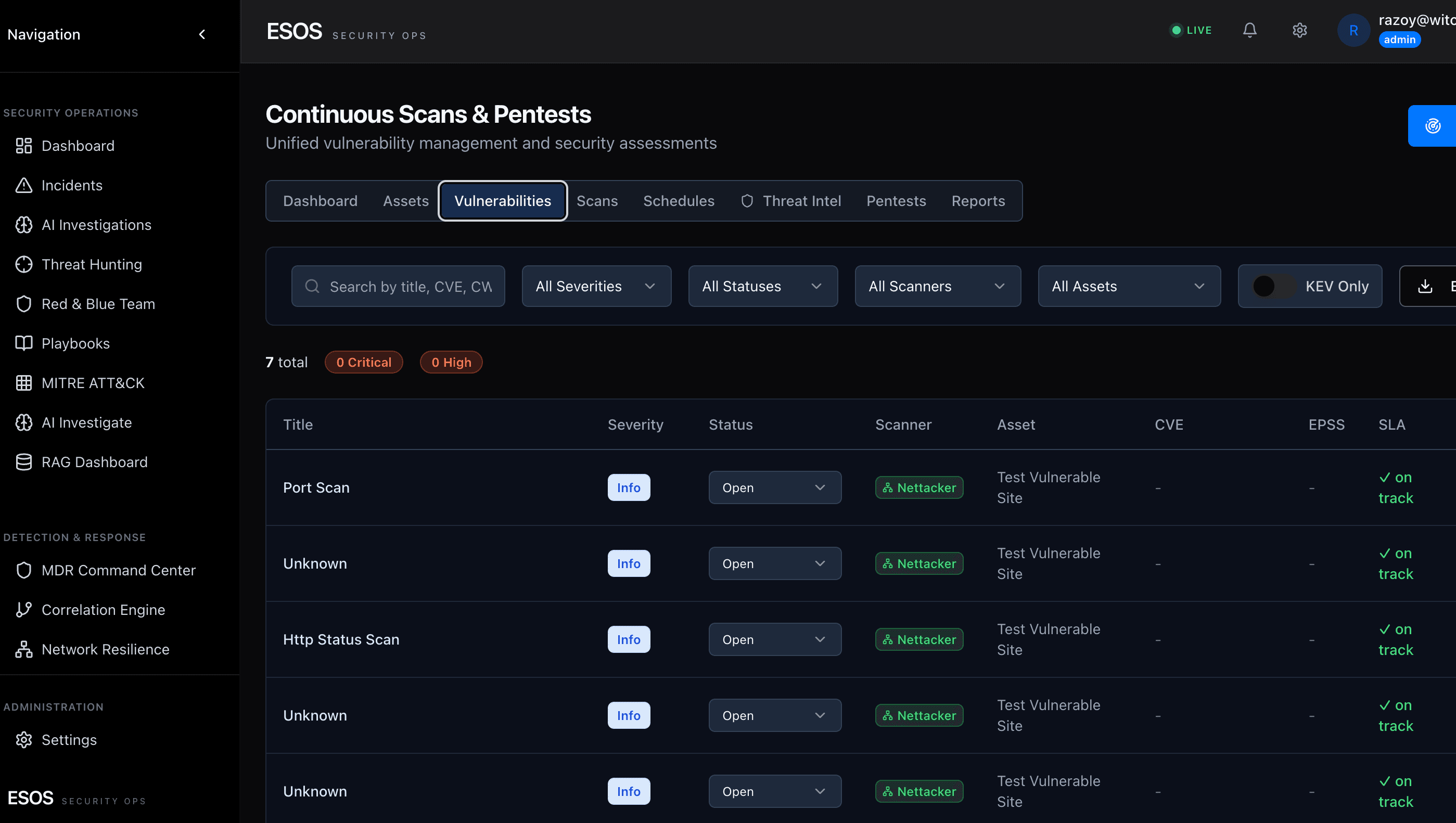
Arctic Wolf's Attack Surface Management discovers what's exposed; the ESOS Vulnerability Management cockpit prioritizes what to fix first. Findings flow between them through WIT OS Flows so one risk score lands in front of your team.
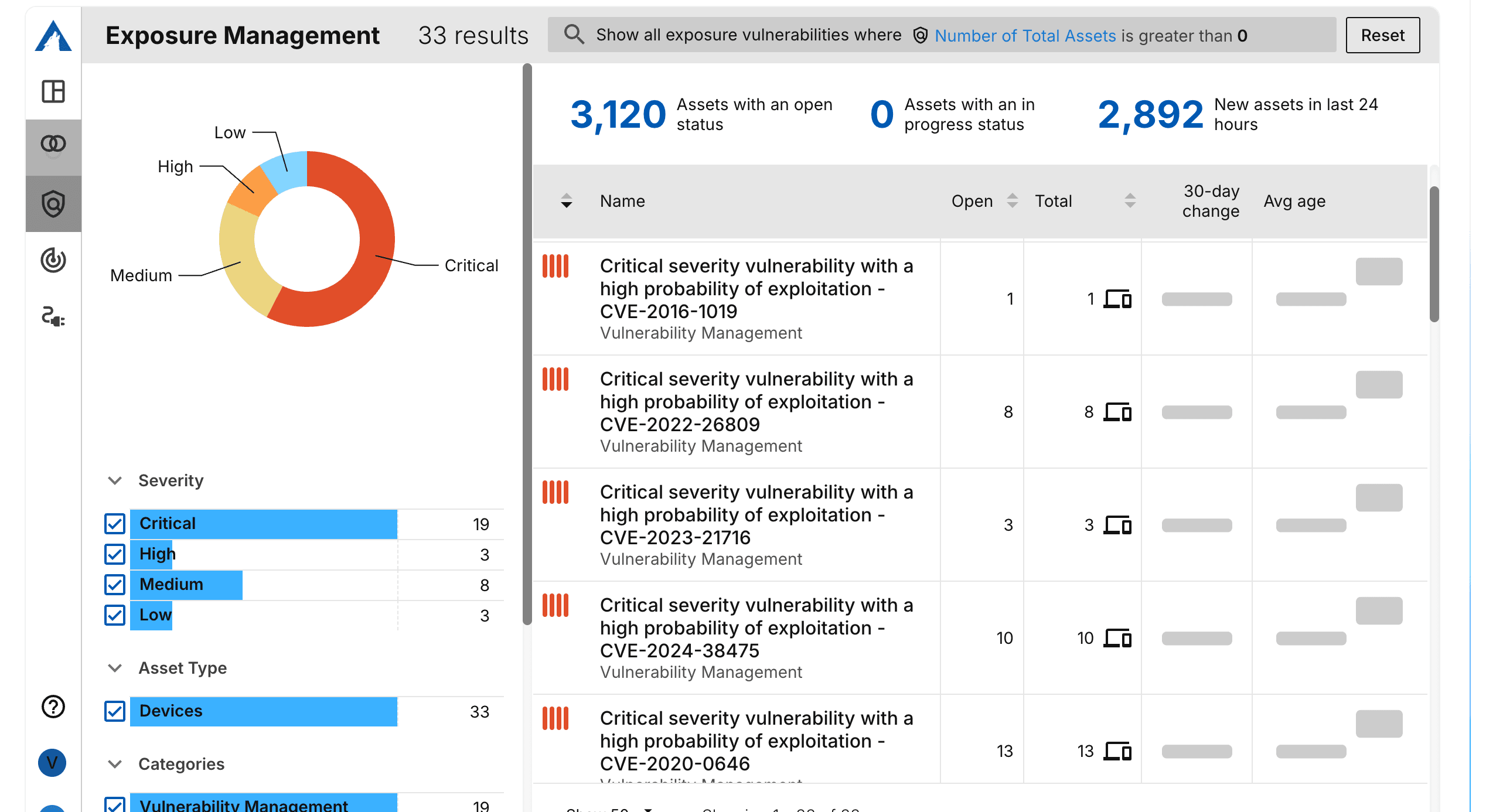
Continuous external + cloud + identity discovery. Concierge Security Team triages new exposures and routes them into the joint engagement.
CVSS · EPSS · KEV · reachability · CMDB criticality reconcile into one prioritization layer. Remediation tickets fire through WIT OS Flows.

Ready to run on WIT OS?
Talk to the team about a managed deployment, a pilot, or a custom agent — we typically respond within an hour.
/ FAQ
Frequently asked questions
Does WIT ONE run its own attack surface management?
No. The Attack Surface Management (ASM) layer is delivered by Arctic Wolf — their Concierge Security Team continuously discovers internet-facing assets, cloud accounts, exposed services, and identity-perimeter surfaces. WIT ONE owns the Vulnerability Management side (built into ESOS) and the joint engagement orchestration. One program, one risk score, two specialist teams.
How does this differ from just having Tenable or Qualys?
Tenable and Qualys are scanners — they tell you what's vulnerable. ESOS Vulnerability Management ingests their output and prioritizes by exploit signal (CVSS + EPSS + KEV), attack-path reachability, asset criticality from your CMDB, and identity exposure. The output isn't a 40,000-row CSV — it's a ranked remediation list with owner, SLA, and one-click ticket creation.
Which scanners do you integrate with?
Tenable, Qualys, Rapid7, Wiz, Snyk, and Aqua are native. The ESOS Vuln Mgmt layer ingests their findings bidirectionally — pulls scan output, pushes back enriched prioritization and ticket status. If your existing scanner isn't on the list, custom connectors ship in 1-2 weeks as part of a customer engagement.
What compliance frameworks does this satisfy?
SOC 2 CC4 (Monitoring), ISO 27001 A.5.7 (Threat Intelligence) and A.8.8 (Vulnerability Management), PCI-DSS Requirement 11 (Vulnerability Programs), HIPAA Risk Analysis, and NIST CSF 2.0 ID.RA. Every scan, finding, remediation, and retest is audit-grade evidence — assembled continuously through WIT OS Flows.